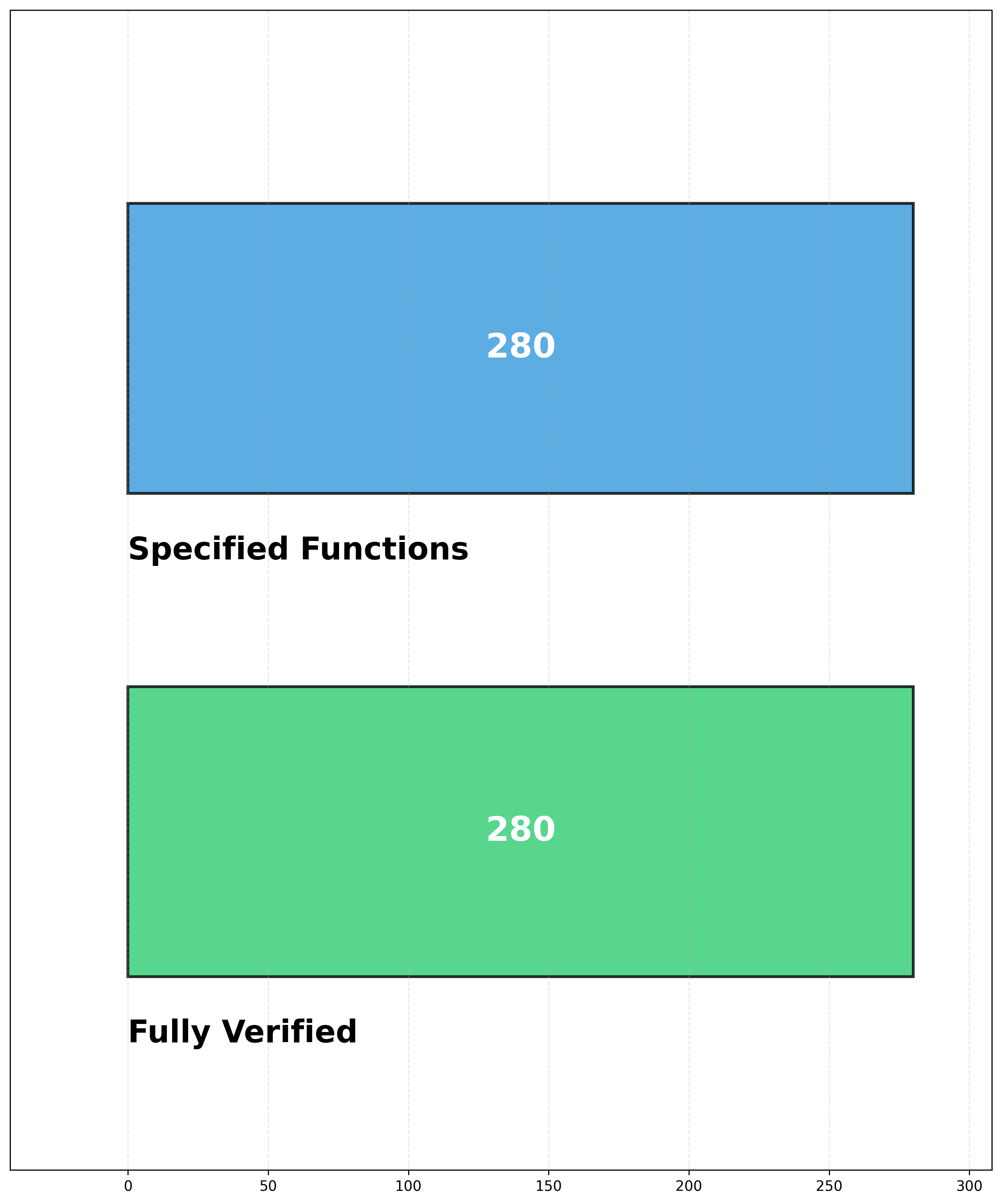
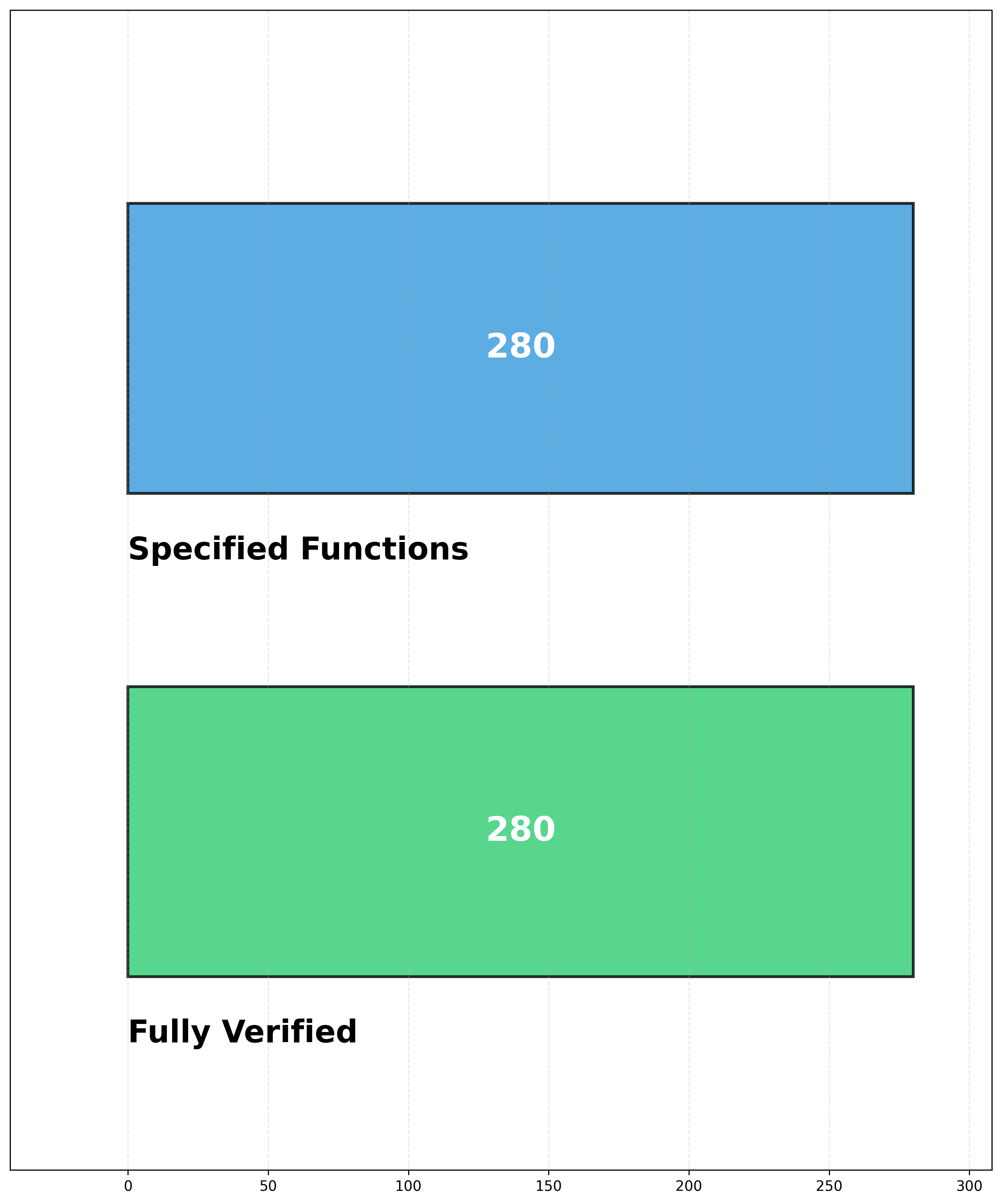
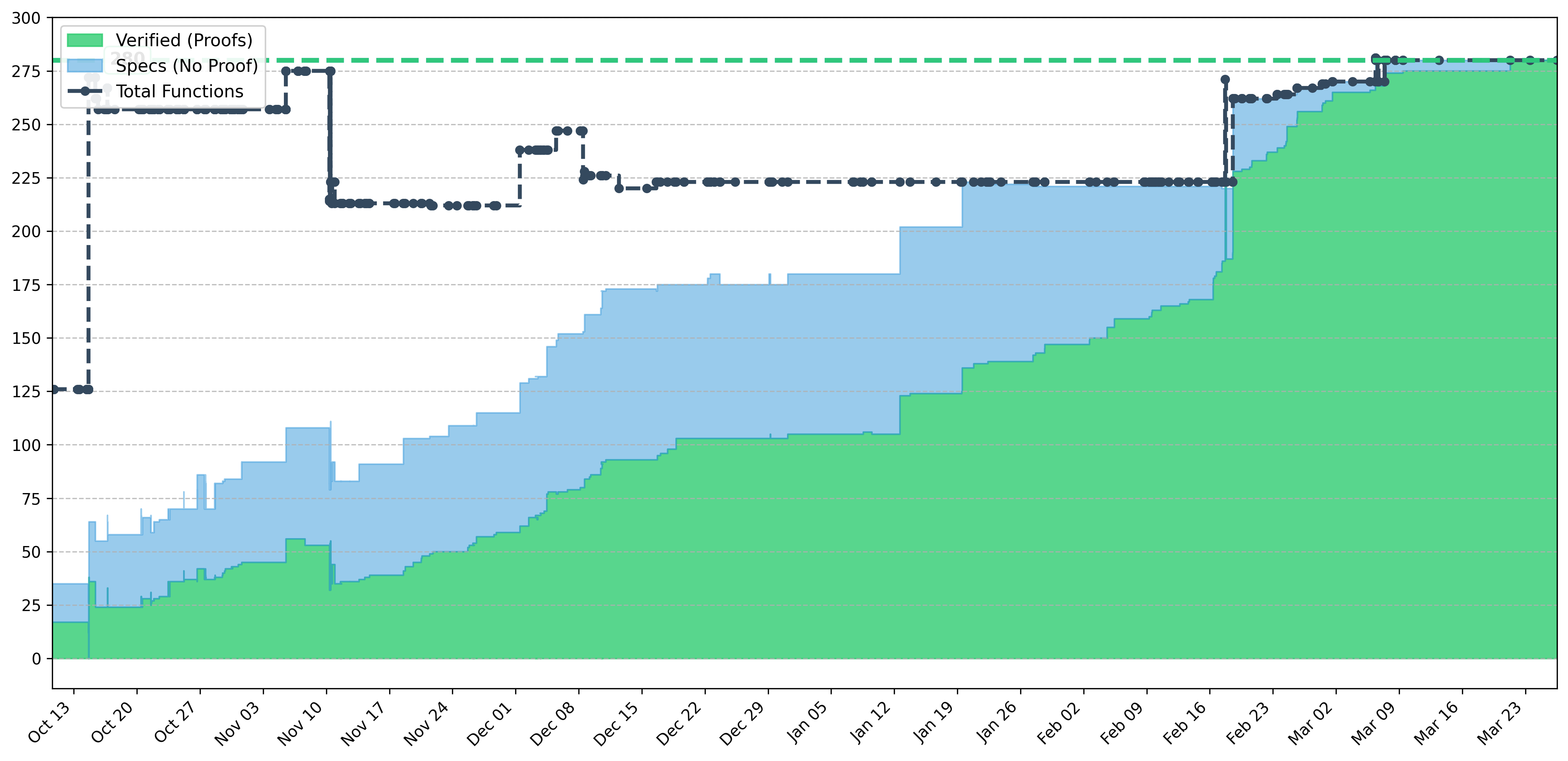
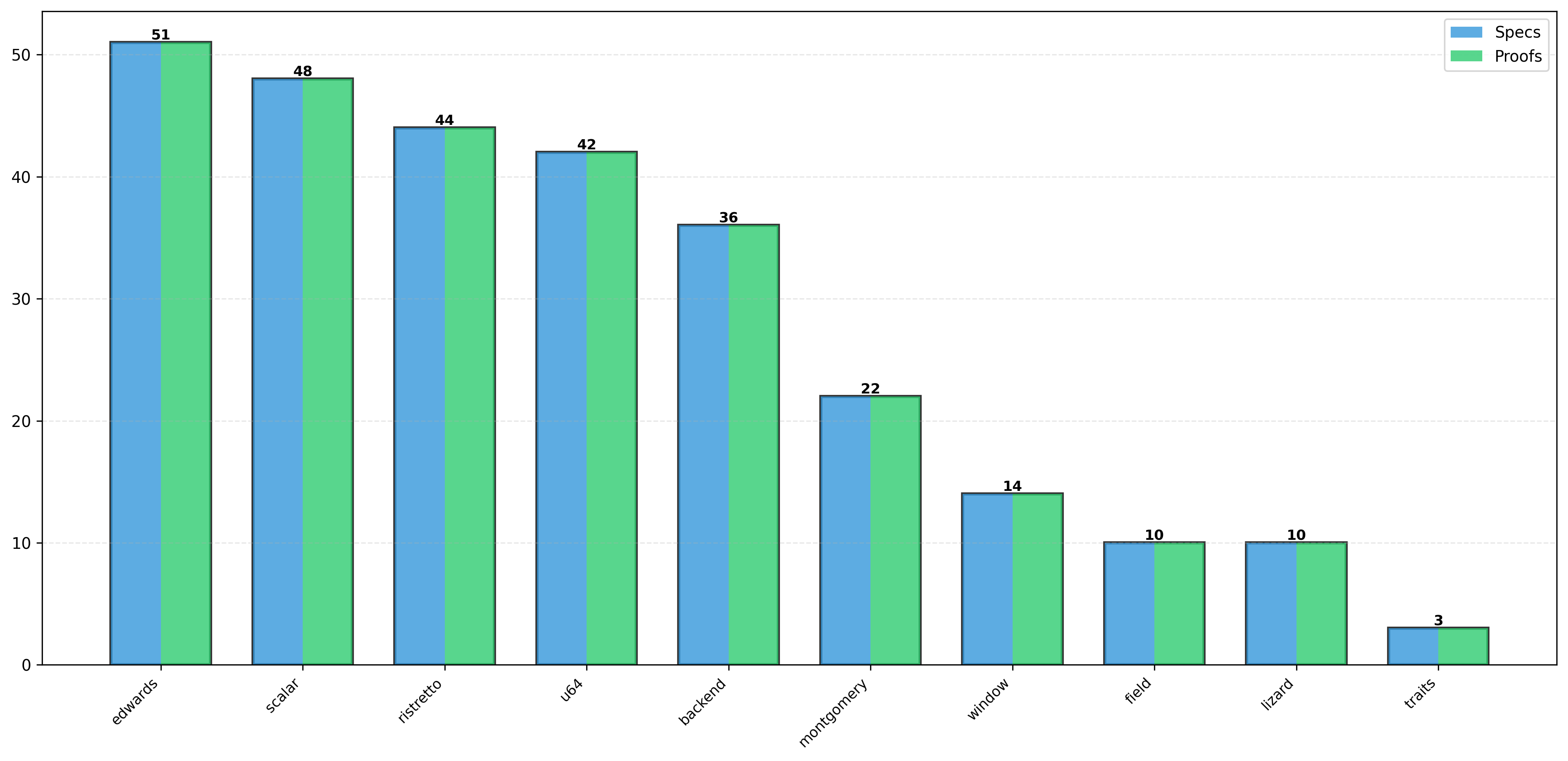
Verification Progress
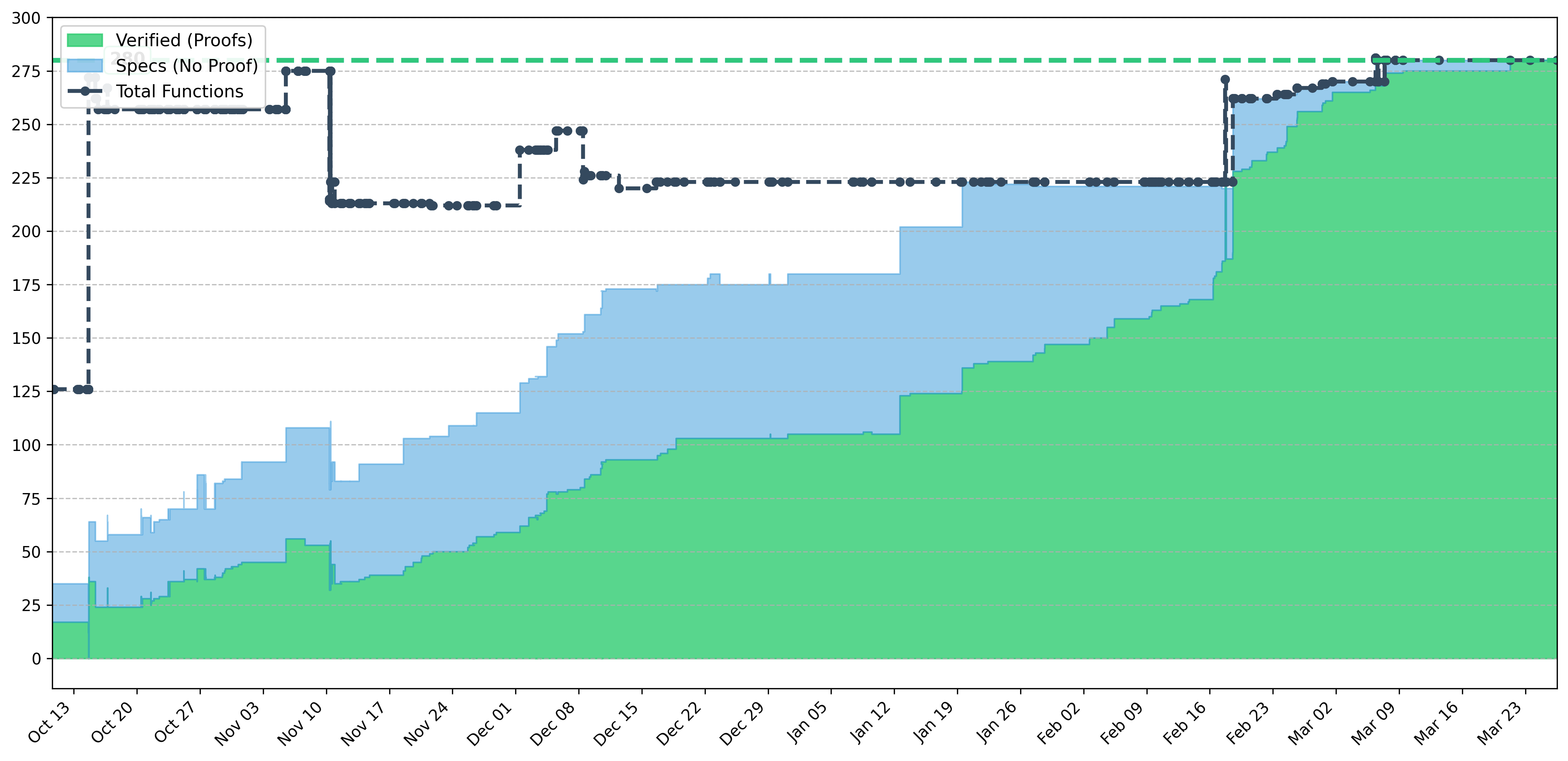
Counts Over Time
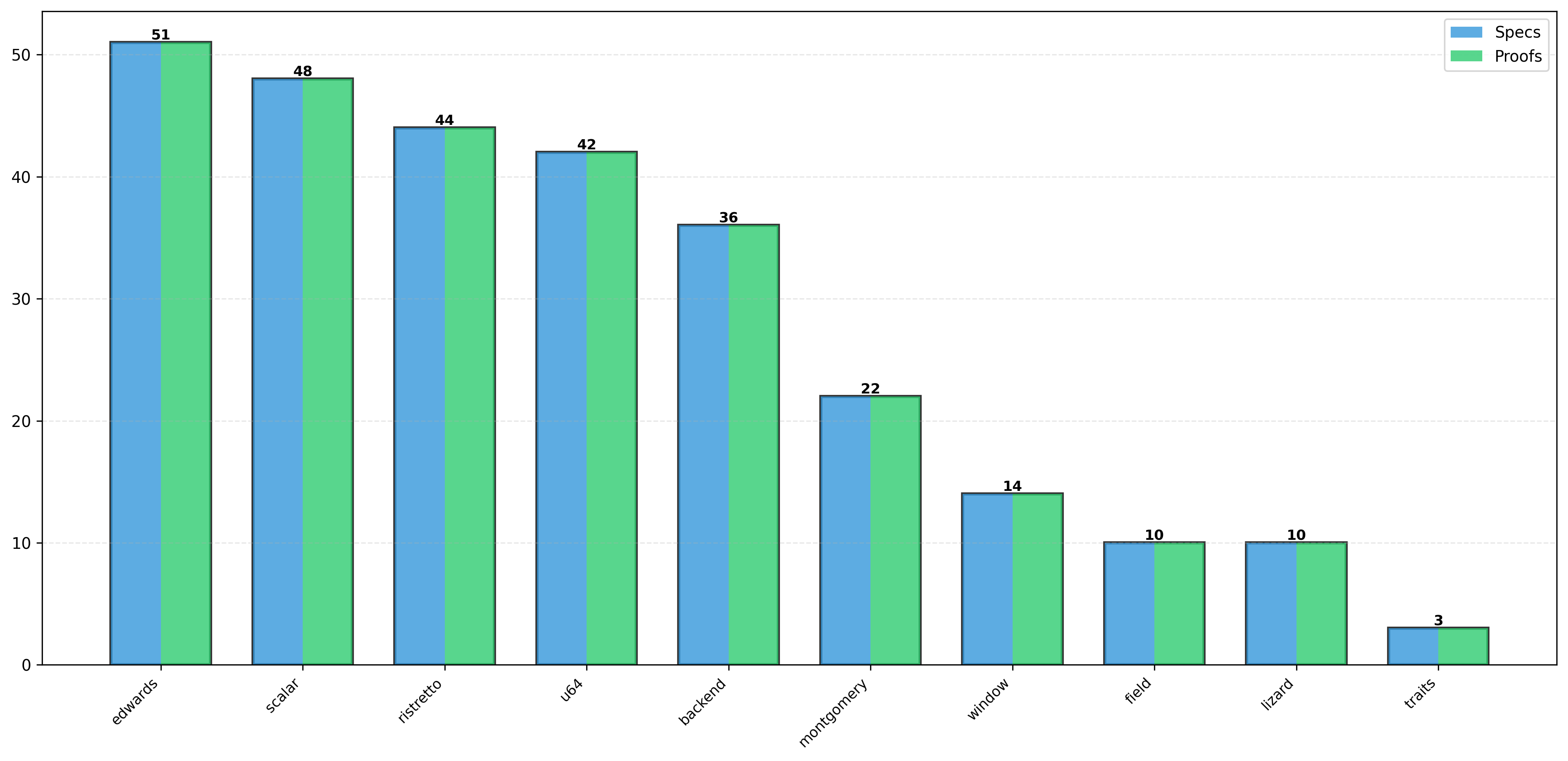
Module Breakdown
Project to formally verify the Rust code of curve25519-dalek using Verus
Formally verify the Rust implementation of curve25519-dalek, a critical cryptographic library used in secure communications worldwide. Our verification uses Verus, a modern verification system designed for Rust.
Verus is a tool for verifying the correctness of code written in Rust. It extends Rust with specification constructs and uses automated theorem proving to verify that implementations match their specifications.
Curve25519-dalek is used by Signal, Tor, and many other security-critical applications. Formal verification provides mathematical proof that the cryptographic operations are implemented correctly, eliminating entire classes of bugs.
To run verification locally:
git clone https://github.com/Beneficial-AI-Foundation/dalek-lite.git
cd dalek-lite
cargo verus verifySee the setup instructions for detailed installation steps.
What we need to trust in order to trust these proofs
We trust that the Verus verification system correctly implements its verification logic and sound reasoning principles.
Verus relies on the Z3 automated theorem prover for checking logical conditions. We trust Z3's implementation of SMT solving algorithms.
We trust that the Rust compiler correctly translates our verified code into machine instructions, and that it respects the semantics Verus reasons about.
We trust that our formal specifications accurately capture the intended behavior of the cryptographic operations.
Like all software, we ultimately trust that the hardware correctly executes the compiled machine code.
We trust the mathematical foundations of elliptic curve cryptography, including the hardness of the discrete logarithm problem on Curve25519.
Verification attestations recorded on the Ethereum blockchain
Each verification run produces a JSON with results. The hash of this JSON is recorded on both Ethereum Mainnet (via Gnosis Safe) and Sepolia testnet for transparency and immutability.
| Date | Commit | Verus | Verified | Content Hash | Mainnet Tx | Sepolia Tx | Artifact |
|---|---|---|---|---|---|---|---|
| Loading certifications... | |||||||
Loading certification data...
Help us verify critical cryptographic code
We welcome contributions! Whether you're experienced with formal verification or just learning, there are ways to help: